protected health information (PHI) or personal health information
What is PHI?
Protected health information (PHI), also referred to as personal health information, is the demographic information, medical histories, test and laboratory results, mental health conditions, insurance information and other data that a healthcare professional collects to identify an individual and determine appropriate care.
The Health Insurance Portability and Accountability Act (HIPAA) of 1996 is the primary law that oversees the use of, access to and disclosure of PHI in the United States. HIPAA defines PHI as data that relates to the past, present or future health of an individual; the provision of healthcare to an individual; or the payment for the provision of healthcare to an individual. HIPAA regulates how this data is created, collected, transmitted, maintained and stored by any HIPAA-covered organization.
Healthcare deals with sensitive details about a patient, including birthdate, medical conditions and health insurance claims. Whether in a paper-based record or an electronic health record (EHR) system, PHI explains a patient's medical history, including ailments, various treatments and outcomes.
What is considered personal health information?
HIPAA lists 18 different information identifiers that, when paired with health information, become PHI. Some of these identifiers on their own can allow an individual to be identified, contacted or located. Others must be combined with other information to identify a person. This list includes the following:
- name;
- address (anything smaller than a state);
- dates (except years) related to an individual -- birthdate, admission date, etc.;
- phone number;
- fax number;
- email address;
- Social Security number;
- medical record number;
- health plan beneficiary number;
- account number;
- certificate or license number;
- vehicle identifiers, such as serial numbers, license plate numbers;
- device identifiers and serial numbers;
- web URL;
- Internet Protocol (IP) address;
- biometric IDs, such as a fingerprint or voice print;
- full-face photographs and other photos of identifying characteristics; and
- any other unique identifying characteristic.
How is PHI used?
From the first moments after birth, a baby will likely have PHI entered into an electronic health record, including weight, length, body temperature and any complications during delivery. Tracking this type of medical information during a patient's life offers clinicians the context they need to understand a person's health and make treatment decisions.
Clinical and research scientists use anonymized PHI to study health and healthcare trends. Researchers can use PHI that is stripped of identifying features and added anonymously to large databases of patient information for population health management efforts. Such anonymized PHI is also used to create value-based care programs that reward healthcare providers for providing quality care.
Hackers and cybercriminals also have an interest in PHI. It is a treasure trove of personal consumer information that they can sell. Criminals also hold PHI hostage through ransomware attacks where they attempt to force a healthcare provider or other organization to provide a payoff in exchange for the PHI.
HIPAA and the Health Information Technology for Economic and Clinical Health (HITECH) Act of 2009 limit the types of PHI healthcare providers, health insurance companies and the companies they work with can collect from individuals. Those regulations also limit what those organizations can do with the data in terms of sharing it with other organizations or using it in marketing. In addition, organizations must provide a patient's protected health information to them if requested, preferably in an electronic PHI (ePHI) format.
What are covered entities under HIPAA
Any organization or individual that handles PHI regularly is categorized under HIPAA as a covered entity and must follow the regulation's security and privacy rules. Healthcare providers and insurers are considered covered entities.
A third party that handles PHI on behalf of a covered entity is considered a business associate under HIPAA and subject to HIPAA rules. For instance, a health information exchange (HIE) is a service that enables healthcare professionals to access and share PHI. Because it is involved in transmitting the PHI on behalf of the covered entity -- the healthcare provider -- the HIE is a business associate and must comply with HIPAA's regulations.
HIPAA privacy rule
The main regulation that governs the secure handling of PHI is the HIPAA Privacy Rule. It governs how hospitals, ambulatory care centers, long-term care facilities and other healthcare providers use and share protected health information. It provides federal protections for PHI that covered entities hold and gives patients certain rights with respect to that PHI. The HIPAA Privacy Rule stipulates when the disclosure of PHI is permitted, such as to ensure the health and safety of the patient and to communicate with individuals the patient says can receive the information.
Organizations cannot sell PHI unless it is one of the following circumstances:
- for a public health purpose that HIPAA allows;
- for research, but only for reimbursement of costs;
- for treatment and payment as allow by HIPAA; or
- as part of the merger or acquisition of a HIPAA-covered entity.
HIPAA also gives individuals the right to make written requests to amend PHI that a covered entity maintains.
Partners of healthcare providers and insurers that sign HIPAA business associate agreements are legally bound to handle patient data according to the HIPAA Privacy and Security Rules. Business associates, as well as covered entities, are subject to HIPAA audits, conducted by the U.S. Department of Health and Human Services' (HHS) Office for Civil Rights (OCR). HIPAA violations are costly and can also damage a business's reputation.
Protected health information was originally intended to apply to paper records. Since the passage of the HITECH Act and the replacement of paper health records with EHRs, HIPAA has increasingly governed electronically stored patient data. HIPAA rules regulate paper and electronic data equally, but there are differences between the two formats.
First, covered entities must respond to patients' requests for access to their data within 30 days, a timeframe created to accommodate the transmission of paper records. However, the HIPAA rules state that if the provider is using health IT technology, the patient may be able to get the records faster.
The disposal methods of PHI also vary between electronic and paper records. Paper files can be shredded or otherwise made unreadable and unable to be reconstructed. Electronic PHI must be cleared or purged from the system in which it was previously held.
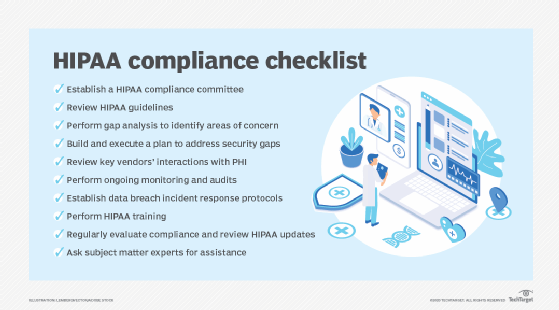
HIPAA compliance and security
The HIPAA Security Rule covers measures that restrict unauthorized access to PHI. Covered entities must defend against threats to PHI that can be reasonably anticipated. It also requires technical, administrative and physical safeguards to protect PHI.
What follows are examples of these three safeguards:
- Technical safeguards cover the use of firewalls, encryption and other technology.
- Physical safeguards include locking up physical records and electronic devices containing PHI.
- Administrative safeguards may include policies that limit PHI access to certain people, safety awareness training and other people-based approaches to security.
Covered entities must evaluate IT capabilities and the likelihood of a PHI security risk. The HIPAA rules does not specify the types of technology to be used, but it should include actions to keep hackers and malware from gaining access to patient data.
Other regulations affecting PHI, include the European Union's General Data Protection Regulation (GDPR). It applies to a broader set of health data, including genetics. Healthcare organizations that treat EU patients must adhere to the GDPR regulations about patient consent to process PHI.
Also, in 2018, the U.S. federal government announced the MyHealthEData program, in which the government promotes the idea that patients should control their PHI and that patients can easily transfer data from one doctor to another. The underlying point of MyHealthEData is to encourage healthcare organizations to pursue interoperability of health data as a way of allowing patients more access to their records.
In December 2020, the HHS proposed changes to HIPAA. Some of the new changes would:
- allow patients to take pictures of or notes on their PHI;
- change the maximum time to provide access to PHI from 30 days to 15 days; and
- permit individuals to request that their PHI be transmitted to a personal health application.
What is the difference between PII, PHI and IIHI?
It's important to distinguish between personally identifiable information (PII) and PHI and a third type: individually identifiable health information (IIHI).
- PII is any data that could potentially be used to identify someone. It can be nonsensitive data that can be transmitted and stored publicly without resulting in harm to the individual. Or it can be sensitive data that, if disclosed, could harm the individual. PII also encompasses more than just health information. It includes information such as tax information, credit card numbers or Social Security numbers used in a context unrelated to healthcare operations and services.
- PHI, by contrast, must be information used in a medical context. Organizations handling PHI must always comply with HIPAA rules. However, protecting PII is only mandated in some instances.
- IIHI is any health information that can identify a person. It is essentially PII in a health context. Not all IIHI is protected under HIPAA. IIHI that has not been transmitted or maintained in some form by a HIPAA covered entity does not qualify as PHI. For example, a patient takes daily blood pressure readings on a form that includes their name, address and phone number but has not yet sent the data to their doctor. That would be IIHI that's not PHI. Although it might be sensitive, because it hasn't been transmitted, it is not protected.
In other words, IIHI becomes PHI if it is:
- transmitted by electronic media, such as email;
- maintained in electronic media, such as on a server; or
- transmitted or maintained in any other form or medium, including on a paper document stored in a physical location.
PHI and healthcare apps
EHRs are a common area where PHI and IT intersect, as are health information exchanges. Vendors create HIE to allow healthcare providers to access and transmit PHI properly. These third-party vendors are responsible for developing applications that are HIPAA compliant.
Developing a healthcare app, particularly a mobile health application, that is HIPAA compliant is expensive and time-consuming. Ensuring that all privacy and security safeguards are in place is particularly challenging. Some developers work with a cloud provider that is certified to host or maintain the parts of the service's stack that need to be HIPAA compliant.
Wearable technology that collects biometric data poses a separate set of challenges when it comes to regulatory compliance and securing PHI. Wearable devices collect a diverse set of information, and it's not always clear which data must be protected. It's also difficult with wearable devices to get properly verified informed consent from users, which is a requirement for most research dealing with healthcare data.
It is generally safe to assume that if an app has anything to do with health information, it will likely have to comply with HIPAA.
More on PHI and wearable devices
Healthcare IoT's next steps come into focus
Wearable health technology and HIPAA: What is and isn't covered
Common misconceptions about PHI
There is some confusion surrounding when healthcare apps must comply with HIPAA. Apps that collect personal health information only conflict with HIPAA in certain scenarios. Some situations where PHI is an issue include the following:
- If a covered entity develops a healthcare app that collects or interacts with PHI, the information must be protected in compliance with HIPAA.
- If a physician recommends that a patient use a healthcare app, the information collected is not covered, because the app was not developed for the physician to use. However, if the data from the app is added to the patient's EHR, it would be covered.
- If a third-party developer makes an app for physicians to use that collects PHI or interacts with it, the information is The third party in this case is a business associate handling PHI on behalf of the physician.
Another area of misinterpretation is that PHI privacy and security do not always move in tandem. It is possible to have security restrictions in place that do not fully protect privacy under HIPAA mandates. For example, if a cloud vendor hosts encrypted PHI for an ambulatory clinic, privacy could still be an issue if the cloud vendor is not part of a business associate agreement. Under HIPAA, the vendor is responsible for the integrity of the hosted PHI, as well as its security.
Also, PHI should not be confused with a personal health record (PHR), which a patient maintains and updates using services such as Microsoft HealthVault or Apple Health. With a PHR patients must oversee the security of the data themselves, akin to consumers guarding their credit card numbers and other personal information. However, the lines between PHR and PHI will blur in the future as more digital medical records are accessed and shared by patients.
Learn how IT tools are being used to capture patient health data in real time to transform the healthcare industry.






