security policy
What is a security policy?
A security policy is a document that states in writing how a company plans to protect its physical and information technology (IT) assets. Security policies are living documents that are continuously updated and changing as technologies, vulnerabilities and security requirements change.
A company's security policy may include an acceptable use policy. These describe how the company plans to educate its employees about protecting the company's assets. They also include an explanation of how security measurements will be carried out and enforced, and a procedure for evaluating the effectiveness of the policy to ensure that necessary corrections are made.
Why are security policies important?
Security policies are important because they protect an organizations' assets, both physical and digital. They identify all company assets and all threats to those assets.
Physical security policies are aimed at protecting a company's physical assets, such as buildings and equipment, including computers and other IT equipment. Data security policies protect intellectual property from costly events, like data breaches and data leaks.
Physical security policies
Physical security policies protect all physical assets in an organization, including buildings, vehicles, inventory and machines. These assets include IT equipment, such as servers, computers and hard drives.
Protecting IT physical assets is particularly important because the physical devices contain company data. If a physical IT asset is compromised, the information it contains and handles is at risk. In this way, information security policies are dependent on physical security policies to keep company data safe.
Physical security policies include the following information:
- sensitive buildings, rooms and other areas of an organization;
- who is authorized to access, handle and move physical assets;
- procedures and other rules for accessing, monitoring and handling these assets; and
- responsibilities of individuals for the physical assets they access and handle.
Security guards, entry gates, and door and window locks are all used to protect physical assets. Other, more high-tech methods are also used to keep physical assets safe. For example, a biometric verification system can limit access to a server room. Anyone accessing the room would use a fingerprint scanner to verify they are authorized to enter.
Information security policies
These policies provide the following advantages.
Protect valuable assets. These policies help ensure the confidentiality, integrity and availability -- known as the CIA triad -- of data. They are often used to protect sensitive customer data and personally identifiable information.
Guard reputations. Data breaches and other information security incidents can negatively affect an organization's reputation.
Ensure compliance with legal and regulatory requirements. Many legal requirements and regulations are aimed at security sensitive information. For example, Payment Card Industry Data Security Standard dictates how organizations handle consumer payment card information. Health Insurance Portability and Accountability Act details how companies handle protected health information. Violating these regulations can be costly.
Dictate the role of employees. Every employee generates information that may pose a security risk. Security policies provide guidance on the conduct required to protect data and intellectual property.Identify third-party vulnerabilities. Some vulnerabilities stem from interactions with other organizations that may have different security standards. Security policies help identify these potential security gaps.
Types of security policies
Security policy types can be divided into three types based on the scope and purpose of the policy:
- Organizational. These policies are a master blueprint of the entire organization's security program.
- System-specific. A system-specific policy covers security procedures for an information system or network.
- Issue-specific. These policies target certain aspects of the larger organizational policy. Examples of issue-related security policies include the following:
- Acceptable use policies define the rules and regulations for employee use of company assets.
- Access control policies say which employees can access which resources.
- Change management policies provide procedures for changing IT assets so that adverse effects are minimized.
- Disaster recovery policies ensure business continuity after a service disruption. These policies typically are enacted after the damage from an incident has occurred.
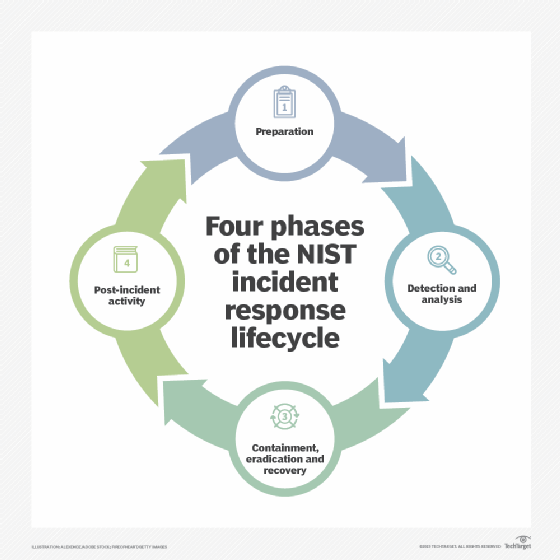
- Incident response policies define procedures for responding to a security breach or incident as it is happening.
Key elements in a security policy
Some of the key elements of an organizational information security policy include the following:
- statement of the purpose;
- statement that defines who the policy applies;
- statement of objectives, which usually encompasses the CIA triad;
- authority and access control policy that delineates who has access to which resources;
- data classification statement that divides data into categories of sensitivity -- the data covered can range from public information to information that could cause harm to the business or an individual if disclosed;
- data use statement that lays out how data at any level should be handled -- this includes specifying the data protection regulations, data backup requirements and network security standards for how data should be communicated, with encryption, for example;
- statement of the responsibilities and duties of employees and who will be responsible for overseeing and enforcing policy;
- security awareness training that instructs employees on security best practices -- this includes education on potential security threats, such as phishing, and computer security best practices for using company devices; and
- effectiveness measurements that will be used to assess how well security policies are working and how improvements will be made.
What to consider when creating a security policy
Security professionals must consider a range of areas when drafting a security policy. They include the following:
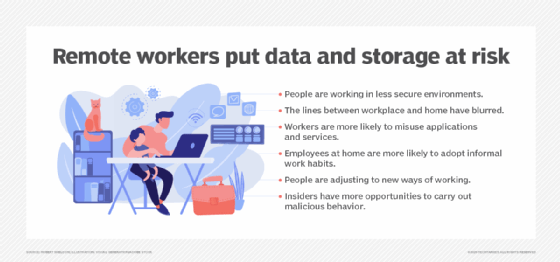
- Cloud and mobile. It is important for organizations to consider how they are using the cloud and mobile applications when developing security policies. Data is increasingly distributed through an organization's network over a spectrum of devices. It is important to account for the increased amount of vulnerabilities that a distributed network of devices creates.
- Data classification. Improperly categorizing data can lead to the exposure of valuable assets or resources expended protecting data that doesn't need to be protected.
- Continuous updates. An organization's IT environment and the vulnerabilities it is exposed to change as the organization grows, industries change and cyberthreats evolve. Security policies must evolve to reflect these changes.
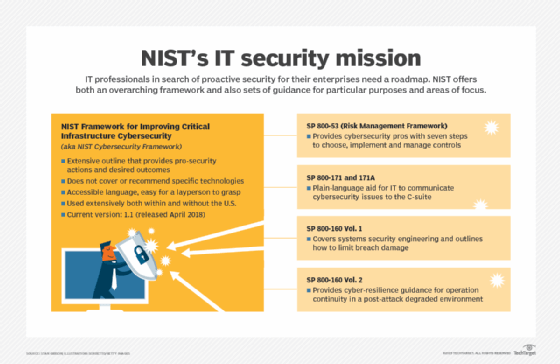
- Policy frameworks. The National Institute of Standards and Technology (NIST) offers its Cybersecurity Framework, which provides guidance for creating a security policy. The NIST approach helps businesses detect, prevent and respond to cyber attacks.
The takeaway
Data is one of an IT organization's most important assets. It is always being generated and transmitted over an organization's network, and it can be exposed in countless ways. A security policy guides an organization's strategy for protecting data and other assets.
It is up to security leaders -- like chief information security officers -- to ensure employees follow the security policies to keep company assets safe. Failing to do so can result in the following:
- customer data in jeopardy;
- fines and other financial repercussions; and
- damage to a company's reputation.
Good cybersecurity strategies start with good policies. The best policies preemptively deal with security threats before they have the chance to happen.
Learn about the top 10 information security threats for IT teams to watch for.








